Making Devices Talk Without Forgetting Their Real Job
Connectivity Is Not the Main Task
Once data has been conditioned and prepared at the edge, it needs to leave the device. This is where connectivity and protocols enter the picture – and this is also where many embedded systems quietly get into trouble.
In theory, communication is just about moving bytes from A to B. In reality, connectivity competes for processing time, memory, power, and attention. For most embedded products, communication is not the main purpose of the system. The device exists to control a motor, regulate a temperature, measure a physical phenomenon, or keep a process stable.
Connectivity is almost always a secondary concern, yet it has a habit of behaving like a primary one if it is not carefully constrained.
Choosing the Communication Layer
The first major design choice is the physical and link layer: wired or wireless, local or wide-area. Ethernet, CAN, RS-485, Wi-Fi, Bluetooth, LTE-M, NB-IoT, LoRaWAN — the list is long, and all come with implicit assumptions about bandwidth, latency, reliability, power consumption, and cost. These assumptions must align with the role of the device.
A control unit running a tight real-time loop has very different tolerance for jitter and blocking behavior than a battery-powered sensor that reports a value once per hour.
On top of the physical connection sits the protocol – and this is where complexity often grows rapidly. Protocols promise interoperability, scalability, and convenience, but they also introduce state machines, buffers, retries, timeouts, and error handling. MQTT, HTTP, CoAP, CANopen, OPC UA are all powerful, but none of them are truly lightweight once implemented robustly.
Even when a protocol is marketed as simple, the edge device must manage connections, recover from failures, and handle unexpected data — all without compromising its primary task.
Security further amplifies the need for boundaries. Encryption, authentication, and certificate handling are mandatory in modern connected products. However, cryptographic operations, TLS handshakes, and key management are computationally expensive and stateful.
If security mechanisms are allowed to interfere with real-time control, the system’s core functionality becomes fragile. Secure communication must therefore be contained within the communication layer and scheduled in a way that cannot disrupt deterministic behavior.
Architecture Must Reflect Priorities
A common mistake is to let communication logic drive the system architecture. When networking code runs in the same execution context as the control algorithm, delays caused by retransmissions, blocking calls, or cloud latency can directly affect system behavior.
These issues rarely appear under ideal conditions. They emerge when networks degrade — exactly when robustness matters most.
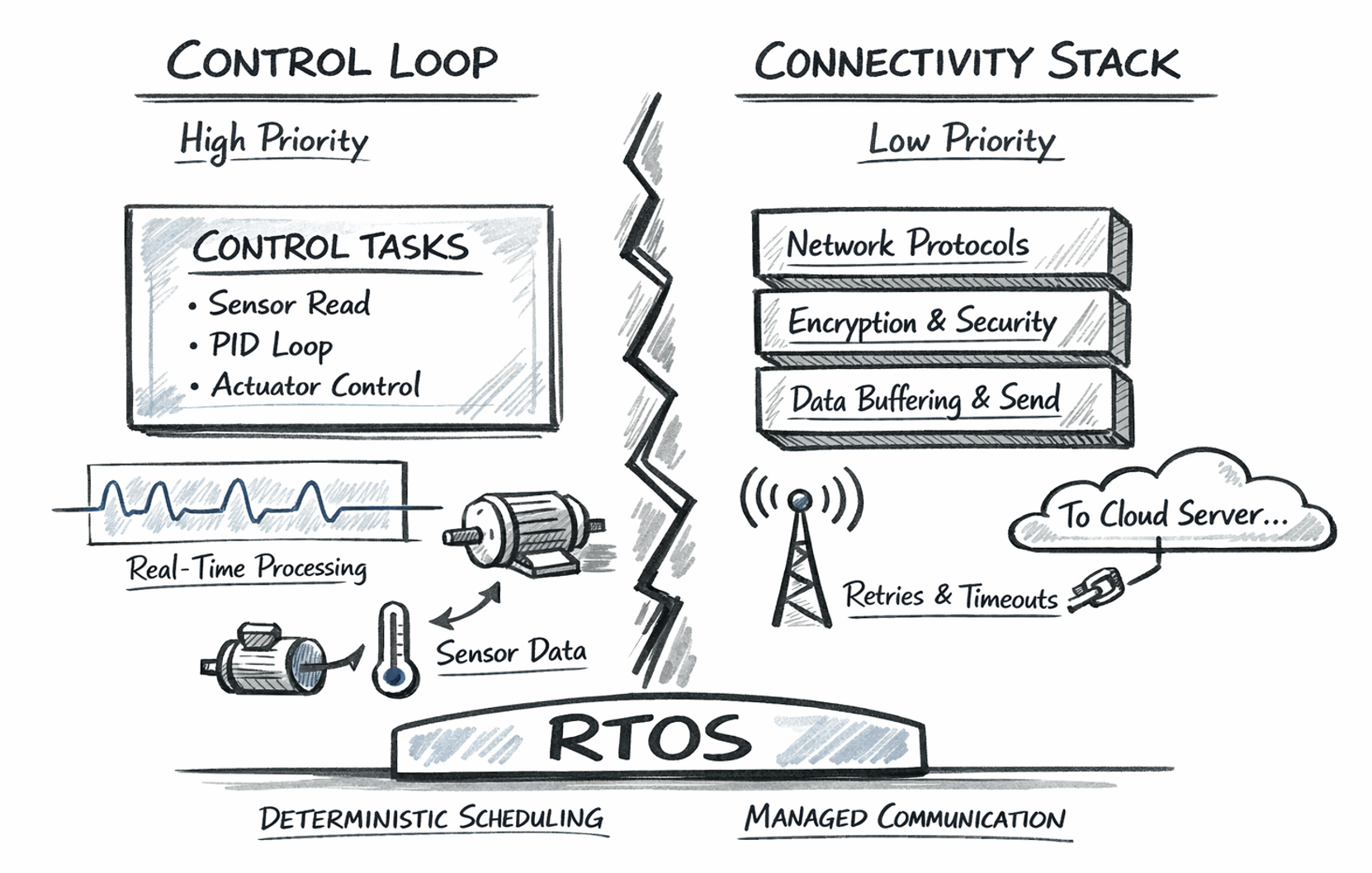
A more resilient approach is to explicitly structure the system around priorities. Time-critical control logic runs in a deterministic, high-priority context. Communication, protocol handling, encryption, and retries operate as lower-priority, best-effort activities. Data is produced according to the needs of the control system and consumed by the communication layer when resources allow.
Maintaining this separation becomes increasingly difficult as systems grow in complexity. Real-time operating system support makes it possible to define priorities explicitly and enforce them through scheduling and well-defined inter-task communication mechanisms. Instead of relying purely on coding discipline, priorities are enforced by design.
Temporary network issues then become a matter of delayed or dropped messages — not degraded control performance.
Connectivity as an Enabler, Not a Risk
Well-designed connectivity at the edge is not about maximizing throughput. It is about enforcing boundaries:
Between real-time control and best-effort communication
Between essential data and optional telemetry
Between what must be sent immediately and what can wait
When these boundaries are clear, connectivity becomes an enabler rather than a liability.
The device remains focused on its primary task, while still providing reliable, secure, and useful data to the outside world. That balance is what turns a connected device into a dependable system instead of just another node on the network.